Privacy
Build trust into every data decision
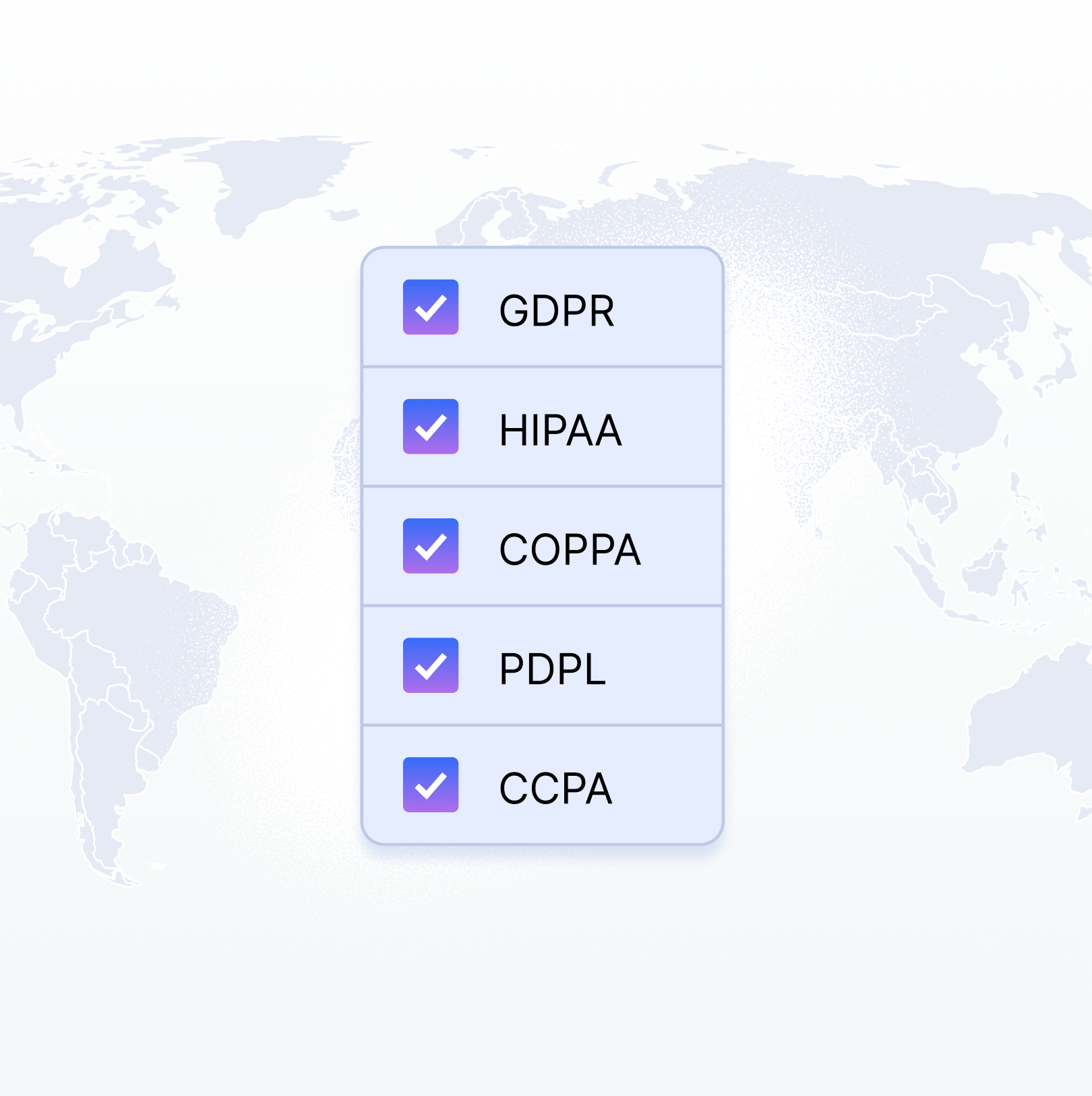
Privacy isn’t a feature - it’s a foundation. Countly is built for organizations that want full control over their data, user trust, and compliance posture. Whether self-hosted or on private cloud, Countly helps you create transparent, secure, and responsible analytics from day one.


Privacy by design, not afterthought
Capturing data is more than just gathering numbers - it’s about ensuring accuracy, completeness, and usability. A well-structured data collection strategy enables seamless integration, minimizes errors, and empowers teams to make confident decisions.



Total control over your data infrastructure
Whether you're in a heavily regulated industry or simply want to own your entire stack, Countly gives you options that match your data governance standards.
On-premise or private cloud
Deploy Countly your way while maintaining full visibility and control.
Encryption and access control
Apply strict data protection policies using enterprise-grade security features.
Regional hosting flexibility
Choose where your data is stored to meet compliance requirements and reduce risk.
ISO 27001 and SOC 2 certified
Countly’s infrastructure and practices are independently audited and certified to meet global security standards.
Build a privacy-first culture
Privacy is also a mindset shared across teams. Countly helps organizations embed responsible data practices into their day-to-day operations.

Role-based permissions
Control who can access what, based on roles, teams, or projects.

Audit trails and access logs
Track every data access or change to ensure accountability and support audits.

Internal standards enforcement
Define and apply organization-wide data collection, retention, and visibility rules so everyone works within the same guardrails.
Transparency you can trust
We take privacy and data protection seriously, and we’re just as committed to transparency around our security and compliance practices.
Our Trust Center offers direct access to our security policies, certifications, audit reports, and real-time system status, all in one place.
Explore our Trust CenterOur Trust Center offers direct access to our security policies, certifications, audit reports, and real-time system status, all in one place.





