The 11 Components of an Effective Data Privacy Checklist
It's hardly groundbreaking to mention the importance of data privacy in the digital world and in business; it's a topic we've previously explored. However, acknowledging its significance is one thing, implementing actionable steps is another. This realization is the inspiration behind our next article.
We at Countly have experienced firsthand that privacy is a competitive advantage rather than merely a compliance checkbox. As a product analytics platform designed from the ground up with data ownership and privacy in mind, we have assisted multinational corporations in navigating this area with control and clarity.
This is not a theoretical checklist. It is based on best practices from the real world, privacy laws like the CCPA and GDPR, and tools we created to support privacy-by-design.
You don’t need to jot anything down or replicate the checklist, as we’ve prepared a downloadable gated version at the conclusion of this article. So, let’s get into it.
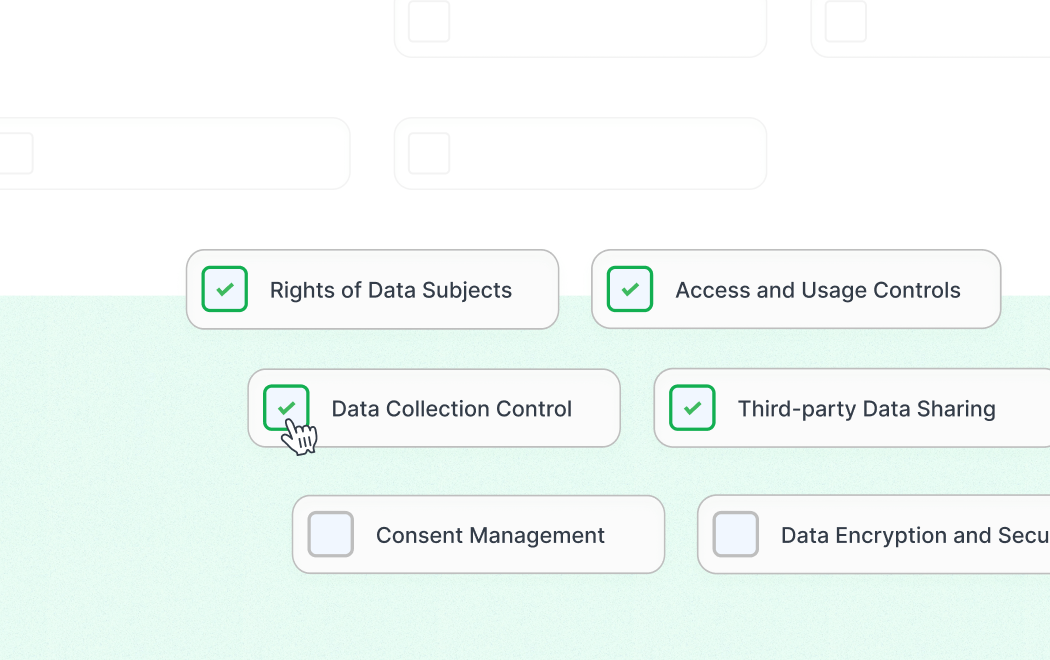
11 Must-have Components of data privacy
These 11 privacy fundamentals are the cornerstones of robust, scalable digital enterprises, not merely suggestions. This checklist helps ensure that your data privacy posture promotes growth rather than friction, regardless of your industry.
1. Consent management
It’s no secret that consent management is a crucial component of data privacy and compliance, especially under regulations like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). Effective consent management ensures that individuals are informed about what data is being collected and how it will be used, providing them with clear choices and expectations.
But there isn’t only one type of configuration. It can be:
- Explicit Consent: Which requires a direct action or statement by the user to indicate consent. It's clear and specific, often used for processing sensitive data or for activities like direct marketing.
Examples:
- Checking a box
- Choosing settings from a menu
- Providing written confirmation
- Implied Consent: This is assumed when a user takes an action that indirectly indicates agreement. It's less explicit than direct consent and isn't sufficient under stricter regulations like the GDPR for sensitive data.
Example: Navigating a website where continued browsing signifies consent to some form of data collection.
- Opt-in Consent: Where users must take an affirmative action to give consent before any data collection occurs. This is considered the gold standard for consent under many data protection laws.
Examples: Selecting a radio button to receive newsletters or opting into tracking cookies on a website.
- Opt-out Consent: Where data collection begins by default, but users are allowed to refuse or stop the data collection.
Example: Pre-checked boxes that users can uncheck if they do not want their data to be collected or the ability to disable certain cookies from a settings menu.
- Granular Consent: It allows users to consent to specific types of data collection and use, but not others. It provides more detailed control over what data is collected and how it's used.
Example: Multiple checkboxes for different types of data processing activities, allowing them to select which they agree to.
Withdrawable Consent: To be fair, consent must be as easy to withdraw as it is to give. Ensuring that users can withdraw their consent at any time is a key component of user rights under data protection laws.
Example: Providing a simple, easily accessible method for users to retract consent, such as a "withdraw consent" button on a website's privacy settings page.
- Dynamic Consent: It is an ongoing and communicative process that can be adjusted at any time according to the user's preferences. It's often used in environments where data use can change over time, such as in research.
Example: Users have a dashboard where they can dynamically adjust their consent options as the scope of data use changes or as new projects arise.
Now that you know the difference and implementations of these consent types, let me tell you what needs to be done to stay on the safe side:
- Implement a user interface for obtaining and recording explicit consent: Create a system where users can easily understand what data you collect and why. The interface should allow them to consent specifically to different types of data processing. Remember to record this consent to ensure compliance and to handle audits.
- Provide clear options for users to manage their consent preferences: Users should be able to change their consent preferences as easily as they gave them. This includes withdrawing consent altogether (withdrawable consent as mentioned above).
2. Data collection control
While that’s not an easy task, data collection control can save your company a lot of headaches. Be it done by product teams, compliance officers, or data protection officers, the important thing is that you:
- Inventory the data types collected to ensure only necessary data is gathered: Regularly review the data you collect to ensure it's strictly necessary for the defined purposes. This minimizes risk and complies with data minimization principles.
- Implement data minimization practices in the data collection process: Only collect data essential for the specific tasks or services. Avoid collecting 'just in case' data that might never be used.
3. Access and usage controls
I have previously answered what can go wrong without data privacy and security in your business, mentioning that lack of data access and usage controls can significantly increase the risk of a data breach.
This can occur through unauthorized access by insiders or external attackers, insider threats where employees misuse data, lack of monitoring that fails to detect suspicious activities, accidental exposure by employees, and external exploitations like malware attacks. So, here is what you need to do:
- Define and enforce roles for who can access analytics data: Restrict data access based on job roles, ensuring that only individuals who need data to perform their jobs can access it
- Set up automatic logs to monitor data access and usage: Implement logging to track who accessed data and what actions they performed. This can later help you in audits and detecting unauthorized access.
4. Third-party data sharing
It’s not enough to be independently privacy-compliant because, sooner or later, you will be part of a more extensive system where sharing data with data processing and analytics tools will be inevitable to transform it into valuable insights. With that being said, you need to:
- Review contracts with third parties to include necessary privacy terms. Before sharing data, ensure that any third-party service providers, especially those involved in data processing and analytics, comply with privacy standards. Contractual agreements should explicitly protect any data shared.
- Develop a checklist for assessing third-party compliance with privacy standards: Regularly evaluate third-party services to ensure ongoing compliance with data protection standards. This assessment should include verifying their privacy policies, security measures, and data handling practices.
5. Data encryption and security
As you may already know, data encryption is a security technique that scrambles readable data into an unreadable format to protect it from unauthorized access. Smartly using mathematical algorithms and keys, encryption ensures that only those with the right key can decode and view the original information. Here is what you need to do in this context:
- Encrypt sensitive data in transit and at rest: Use strong encryption to protect data from unauthorized access. This applies when data is being transmitted and when it's stored.
- Schedule regular updates for security software: Keep security systems up-to-date to protect against vulnerabilities and threats.
6. Retention policy implementation
Simply put, a data retention schedule outlines how long different types of data are stored and the methods for their secure disposal once they're no longer needed. It includes identifying the types of data held, specifying the purpose and legal basis for retention, defining the retention periods based on these criteria, detailing how and where data is stored, describing who has access, and explaining how data is securely deleted. So in summary, this implies:
- Establishing a data retention schedule and mechanisms for data deletion: Specify how long different data types are retained and establish automated processes to delete no longer necessary data.
- Automating the purging of old data according to the retention policy: Use automated systems to ensure data is deleted as scheduled, preventing unnecessary data accumulation.
7. Rights of data subjects
Before you check these items from the list, let me refresh your memory on what a “data subject” is. According to AI Internet’s glossary, a data subject is an individual who can be identified, directly or indirectly, by personal data. This personal data might include names, identification numbers, location data, online identifiers, or factors specific to that individual's physical, physiological, genetic, mental, economic, cultural, or social identity.
Simply put, if information can uniquely identify a person, that person is considered a data subject in the context of data protection and privacy laws. So, how do you protect the rights of data subjects? You do so by:
- Creating a user portal for data access requests: Allow users to view, request, and manage their data through a secure online portal.
- Automating the response process for user data modification and deletion requests: Implement systems that can automatically handle requests to change or delete personal data, making the process efficient and compliant.
8. Privacy Impact Assessments (PIA)
I assume you’ve only got this far in the article because you are serious about data privacy in your business. If so, you need to remember that a Privacy Impact Assessment (PIA) is a crucial tool for your company to proactively manage privacy risks associated with new and existing services or products.
It helps identify and reduce a project's privacy risks by analyzing how personal information is handled, ensuring that the project complies with privacy laws, and identifying any potentially invasive aspects that might cause trouble among your users or the public.
Here is a full guide on how to conduct a Privacy Impact Assessment, and here is how it can be actionable within the checklist:
- Integrate regular privacy impact assessments into product development cycles: Conduct assessments to identify potential privacy risks when introducing new products, services, or business practices.
- Document any identified risks and implemented mitigations: Keep records of risks and how they are mitigated to inform future decisions and demonstrate compliance.
9. Training and awareness
Data privacy within your company should be more of a mindset than just a set of rules to follow. Cultivating a culture where data protection is deeply ingrained ensures that every employee is responsible for the data they handle. To support this culture, ongoing training and communication are essential:
- Organize quarterly data privacy training for all relevant employees: Ensure all employees understand the importance of data privacy and how to implement it in their roles.
- Distribute monthly newsletters on privacy best practices and updates: Keep the team informed about new privacy regulations and internal policy changes.
10. Privacy policy and communication
This one is simple. You don’t want your privacy policy to be outdated, causing miscommunication and confusion, right? So make it a habit to:
- Update the privacy policy to reflect current practices and ensure clarity: Regularly review and update it to keep it accurate and transparent to users.
- Establish a dedicated channel for privacy questions and complaints from users: Provide a specific point of contact for users to raise privacy concerns, enhancing trust and transparency.
11. Audit and compliance checks
Finally, after it’s all done, don’t forget to maintain the effort you have made and stay consistent. You can do this by:
- Conducting an annual internal or third-party audit of privacy practices: Regular checks ensure practices are up to standard and reveal areas for improvement.
- Reviewing and updating compliance documentation as needed: Keep all documentation relevant and up-to-date to support compliance efforts and prepare for audits.
Logs include drill bookmarks, configuration changes, and more, giving compliance teams the evidence they need for internal reviews or regulatory audits.
Where Countly fits into data privacy
Countly supports businesses aiming to implement privacy-by-design, but please don’t mistake it for a specialized data privacy platform. Instead, Countly is a product analytics platform that helps teams analyze product data safely while complying with legal standards and respecting customer privacy choices.
Find out how Countly supports the following values mentioned in the above checklist, with added insights from our CTO, Arturs Sosins:
Privacy-conscious features
- Consent Awareness: Analytics teams can use Countly to respect user consent in their tracking logic. It records opt-in and opt-out rates according to established standards. However, it does not handle consent interfaces or take integrator-provided custom tracking definitions.
- Data Suppression & Minimization: Helps teams gather only the essential information by providing tools to suppress or redact sensitive data.
“Tracking everything is not a cost-effective solution. You need to plan and control what data you collect. Countly provides data governance tools where you can see all the data you are collecting and manipulate it, like edit, delete, block, redact, or mask it from some users.”
- Controls over access and audits: Role-based access and logging ensure that only the right people may access sensitive information, and every action can be tracked, which is helpful for audits.
- Self-Hosting for Data Ownership: By enabling businesses to store and control all analytics data on their own infrastructure, Countly may be completely self-hosted, preventing exposure to third parties.
“There are two options. The first one is self-hosting, when a customer takes Countly software, installs it, and manages it on their servers. Countly cannot access those servers or see any data in that case. You are in full ownership of the data.”
“The second option is to outsource server resource management to Countly. Contractually, you still own the data and have full access to it, but the server resources are monitored and measured by the Countly team.”
- Encryption: Data is encrypted both in transit and at rest.
“Countly handles data security and encryption to protect first-party data through standard practices of data encryption during transfer and at rest. So nobody can access it while it is transferred. And when it is stored, even if it is stored on the Cloud, for example, people working for the Cloud company would not be able to access it.”
- User Rights & Data Portability: This helps you comply with the rights of data subjects under the CCPA and GDPR by offering options for data export and deletion.
- Supporting Resources: Countly provides documentation and guidance to assist teams in comprehending and putting best practices for privacy-conscious analytics into practice, even though it is not a training platform.
Final note
Countly is one of many tools an organization should use in a privacy-focused tech stack. Its value lies in enabling secure, respectful, and transparent product analytics.
Your next steps towards data privacy success
Privacy is not just a project; it's a commitment and a mindset. This checklist is your roadmap for building a robust, reliable company that adheres to regulations.
Each of the 11 components is crucial for transforming privacy from a mere checkbox into a competitive advantage, whether that involves proactively monitoring third-party risks, avoiding unnecessary data collection, securely encrypting information, or managing consent in a dynamic and user-friendly way.
Now that you have a framework, you can assess your privacy position, identify gaps, and implement significant adjustments. Your goals should be progress and responsibility rather than perfection.
It's important to understand that no single team or tool can fully "own" privacy. The duty falls collectively on legal, product, engineering, marketing, and support teams. This collaborative effort should be evident in your infrastructure. You can employ multiple tools, such as Countly, to support this strategy. Countly enables the respectful and transparent collection and analysis of user data, acting as a privacy-focused product analytics platform that upholds full ownership.
The summarized checklist is available below as a downloadable resource to help guide your next steps.