How to implement crash analytics in a Healthcare App Without Exposing Patient Data
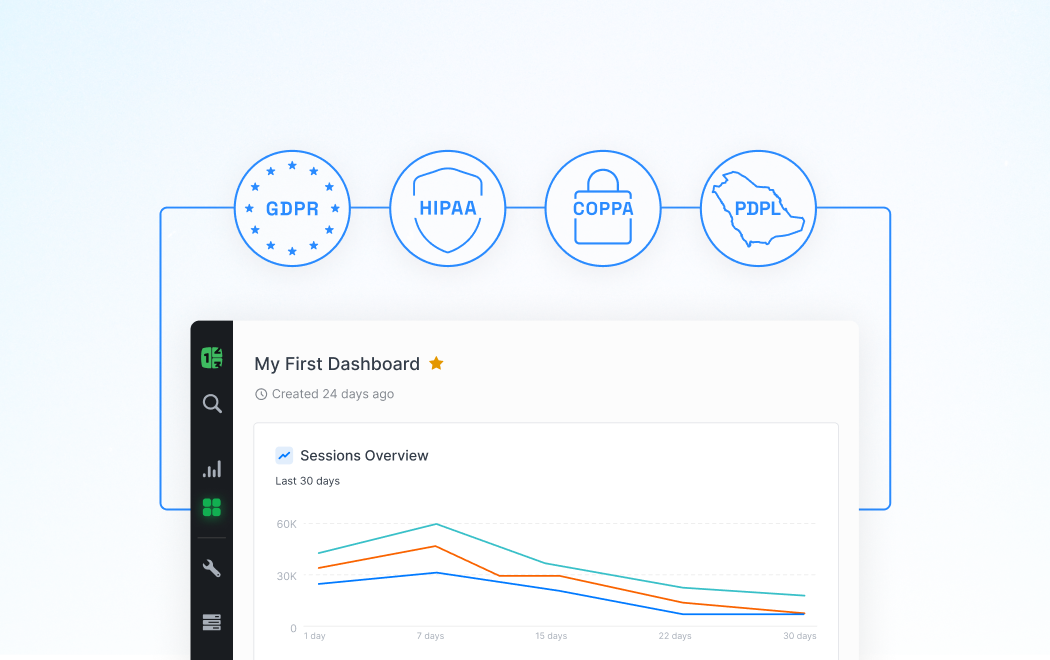
Healthcare apps handle some of the most sensitive data imaginable, yet they still crash like any other software. The challenge for developers is that traditional crash analytics tools collect context that can inadvertently capture protected health information (PHI), creating HIPAA violations before you even realize what's been logged. This guide walks through the technical approaches that let you diagnose crashes effectively while keeping patient data completely isolated from your analytics pipeline.
Understanding the PHI Risk in Standard Crash Reporting
Most crash analytics SDKs are built for general-purpose apps and collect everything they can by default. When a healthcare app crashes, the stack trace might reference a patient ID in a variable name, the device state could include clipboard contents with medical notes, or custom events leading up to the crash might contain appointment details. According to the U.S. Department of Health and Human Services, unauthorized disclosures of PHI affected over 133 million individuals between 2009 and 2023, with technical vulnerabilities representing a significant attack vector that includes improper data handling in third-party services.
The problem compounds because crash reports often get stored on third-party servers where your Business Associate Agreement (BAA) might not extend. Even if your main database is HIPAA-compliant, that crash report sitting in an analytics vendor's infrastructure without a proper BAA creates liability. Developers frequently assume that pseudonymized data is safe, but HIPAA's definition of PHI includes any information that could reasonably be used to identify an individual, which can include combinations of timestamp, device type, and usage patterns that seem innocuous in isolation.
The technical architecture of most crash reporting tools wasn't designed with healthcare's regulatory requirements in mind. They prioritize comprehensive data collection to aid debugging, which directly conflicts with the principle of data minimization required under HIPAA. This means you need to either heavily customize a general analytics platform or choose tools specifically designed for regulated industries, then implement additional safeguards at the code level to prevent PHI from ever reaching the crash reporting pipeline.
Implementing Data Scrubbing at the Application Layer
The first line of defense is sanitizing data before it ever touches your crash analytics SDK. Create wrapper functions around any logging or error handling that automatically strip known PHI patterns using regular expressions for medical record numbers, patient identifiers, and clinical values. This preprocessing layer should run synchronously during crash handling so that even if your app terminates unexpectedly, the sanitization has already occurred on data that gets persisted.
Consider implementing a whitelist approach for custom metadata rather than trying to blacklist all possible PHI. Define explicitly what contextual information is safe to attach to crash reports—things like app version, generic screen names, and sanitized error codes—and reject everything else. This requires more upfront design work but dramatically reduces the risk of accidentally logging a field that contains patient information. Your crash handling code should validate that any custom key-value pairs being attached match the approved schema before the report gets sent.
Environment variables and configuration values also need scrutiny because developers sometimes store database connection strings or API keys that could provide access to PHI in ways that aren't immediately obvious. Implement runtime checks that scan crash metadata for patterns that look like credentials or personally identifiable information, and replace them with placeholder values. Some crash analytics platforms including Countly allow you to configure server-side scrubbing rules as an additional layer, but client-side prevention is more reliable because it reduces what ever leaves the device.
Architecting Session Replay and Breadcrumb Trails Safely
Session replay features that record user interactions before a crash are particularly dangerous in healthcare contexts. If your analytics platform offers this capability, it should be completely disabled for any screens that display PHI, which in healthcare apps is almost everything. The technical implementation requires explicitly marking view controllers or components as sensitive and ensuring your analytics SDK respects these flags to stop recording when these screens are active.
Breadcrumb trails that log user navigation and actions can be made safe by using generic identifiers rather than descriptive labels. Instead of logging "Viewed John Doe's medication list," log "Viewed patient detail screen" with a sanitized screen identifier. The same principle applies to user actions—"Updated prescription" is safe while "Updated prescription for Metformin 500mg" contains clinical information that shouldn't be in crash reports. This requires discipline in how you instrument your code and regular audits to ensure new features maintain these boundaries.
The timestamp granularity in breadcrumbs deserves attention as well. While knowing that a crash occurred 200 milliseconds after a specific action is useful for debugging, combining precise timestamps with other metadata can potentially re-identify patients through their unique usage patterns. Consider rounding timestamps to the nearest second or using relative time offsets from session start rather than absolute times. This preserves the sequential relationship between events that caused the crash while reducing the uniqueness of the data.
Configuring Server-Side Processing and Storage Controls
Once crash data leaves the device, your server-side infrastructure must enforce the same privacy boundaries. If you're using a crash analytics platform, verify that you have a signed BAA and that the vendor's infrastructure meets HIPAA security requirements including encryption at rest and in transit. The vendor should also support data residency requirements if your organization has policies about where PHI-adjacent data can be stored geographically.
Configure your analytics platform to automatically expire crash reports after the minimum retention period needed for debugging. HIPAA doesn't prescribe specific retention periods for crash logs, but the principle of keeping data only as long as necessary applies. A 90-day retention policy gives you time to identify and fix issues while limiting exposure. Some platforms let you automatically delete crash reports once the associated issue is marked as resolved, which further reduces your data footprint.
Implement access controls that limit who in your organization can view crash reports, treating them with similar sensitivity to application logs that might contain PHI. Use role-based access control to ensure that only developers actively working on debugging have access, and maintain audit logs of who accessed which crash reports and when. Even though your scrubbing should prevent PHI from appearing in crashes, the combination of multiple crash reports from the same user could still reveal patterns that warrant restricted access.
Common Mistakes When Integrating Crash Analytics
The most frequent error is enabling all features of a crash analytics SDK without reviewing what each one collects. Developers install the SDK, follow the quick-start guide, and assume the default configuration is appropriate for healthcare apps. In reality, features like automatic screenshot capture on crash, full network request logging, and environment variable collection need to be explicitly disabled. Take time to read through the SDK's privacy settings documentation and create a hardened configuration template that all developers use.
Another common mistake is inconsistently applying sanitization logic across the codebase. One team might carefully scrub PHI from error messages while another team working on a different feature logs sensitive data through custom events without realizing it feeds into the same crash analytics pipeline. Establish code review guidelines that specifically check for PHI exposure in logging and error handling code, and consider building linting rules that flag suspicious patterns like logging variables that match patient identifier naming conventions. Creating shared utility functions for logging ensures that sanitization logic is applied uniformly rather than reimplemented differently across modules.
Building a Sustainable Privacy-First Analytics Practice
As your healthcare app evolves, maintaining the separation between useful debugging information and PHI requires ongoing vigilance rather than a one-time configuration. Establish a quarterly review process where you audit your crash analytics implementation against your current understanding of what constitutes PHI in your specific application context. Healthcare regulations and your app's features both change over time, and assumptions that were safe six months ago might not hold today. This review should include sampling actual crash reports to verify that scrubbing is working as intended and no sensitive data is slipping through.
Consider investing in synthetic data generation for your crash testing and debugging workflows. By creating realistic but fake patient data for testing environments, you can enable more comprehensive crash debugging tools in non-production settings without risk. This lets developers use full-featured analytics during development and QA while maintaining strict data minimization in production. The synthetic data should be clearly marked as such in your database so that any crash reports from test environments are immediately identifiable and don't get mixed with production issues.
Key Takeaways
• Default crash analytics configurations collect too much context for healthcare apps and must be hardened through both client-side scrubbing and server-side controls to prevent PHI exposure.
• Implement data sanitization before crash reports are created using whitelist approaches and explicit validation of what metadata can be attached to error logs.
• Disable features like session replay and detailed breadcrumbs on screens displaying PHI, replacing descriptive labels with generic identifiers that preserve debugging utility without capturing sensitive data.
• Verify your crash analytics vendor has a signed BAA, supports HIPAA-compliant infrastructure, and configure appropriate data retention and access controls for all crash reports.
Sources
[U.S. Department of Health & Human Services - Breach Portal](https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf)
[HIPAA Journal - Protected Health Information](https://www.hipaajournal.com/what-is-protected-health-information/)
[Countly Healthcare Analytics Documentation](https://support.count.ly/hc/en-us/categories/360002067291-Industries)
FAQ
Q: Can I use crash analytics at all in a HIPAA-compliant healthcare app?
A: Yes, but you need to implement it carefully with data scrubbing, proper vendor agreements, and restricted feature sets. The key is ensuring that crash reports contain only the technical information needed for debugging while completely excluding any PHI. Many healthcare apps successfully use crash analytics by treating it as a covered function that requires the same privacy safeguards as other systems handling patient data.
Q: What specific SDK features should I disable for healthcare apps?
A: Disable automatic screenshot capture, full session replay, clipboard content logging, environment variable collection, and detailed network request logging that might include API payloads. Also turn off automatic attachment of user-entered data from forms and any features that capture console logs without sanitization. Each SDK structures these features differently, so review your specific platform's documentation to identify all data collection mechanisms.
Q: How do I know if my crash scrubbing is working correctly?
A: Implement automated testing that deliberately triggers crashes in test environments with PHI present and verifies the resulting crash reports contain no sensitive data. Manually review a sample of production crash reports quarterly to audit for any PHI that might have bypassed your scrubbing logic. Consider setting up alerts that scan crash report text for patterns matching medical record numbers or other identifiers, though this should be a backup to prevention rather than your primary control.